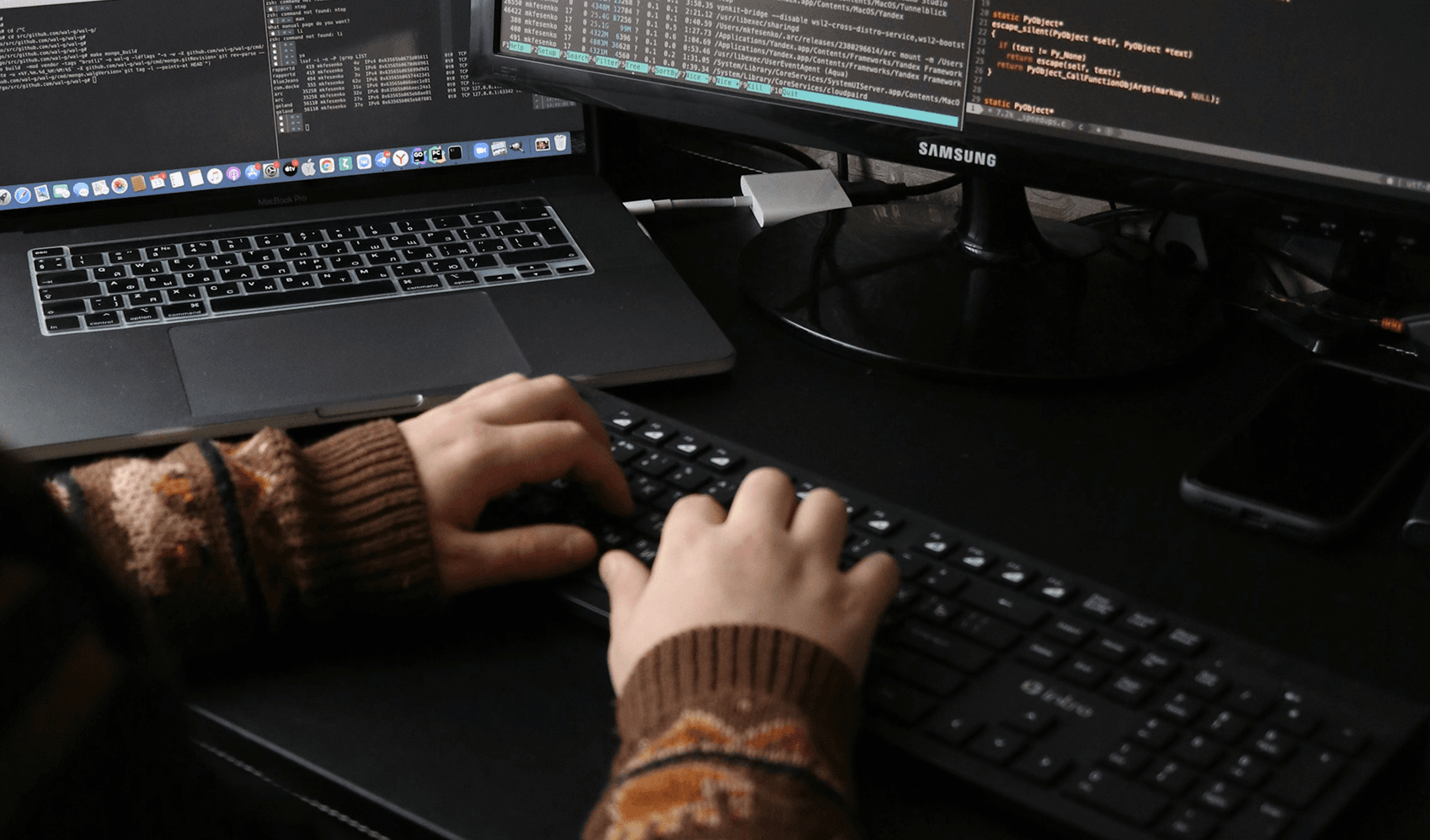
Securing your pipeline from
modern threats.
Integrate security into every stage of your CI/CD pipeline — protecting applications, infrastructure, and data against real-world attacks.
Security woven into
every pipeline
Auster Cyber Tech embeds security into the heart of your development lifecycle. We don't bolt on protection after the fact — we engineer it into every commit, build, and deployment.
Our DevSecOps engineers bring deep expertise in cloud-native architecture, container orchestration, and automated security tooling — ensuring your teams ship fast without sacrificing safety.


Years securing cloud-native development pipelines

Pipelines secured & hardened

Faster vulnerability remediation
Automated scanning & real-time alerting

Pipeline-Native Security
Security gates woven directly into CI/CD — from commit hooks to production deploy, every stage is hardened.

Cloud & Container Experts
Kubernetes, Docker, AWS, Azure, GCP — we secure your workloads wherever they run, at any scale.

Shift-Left Automation
SAST, DAST, SCA, and IaC scanning automated from the first pull request — catch flaws before they ship.

Compliance as Code
Policy-as-code guardrails enforce SOC 2, ISO 27001, and NIST controls continuously — not just at audit time.
We design, secure, monitor, and maintain pipelines to prevent unauthorized access, data breaches, and downtime.

We secure your entire CI/CD pipeline from code commit to production deployment, integrating automated security gates, secret scanning, and vulnerability checks at every stage.
Learn More→Lorem ipsum dolor sit amet, consectetur adipiscing
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod Lorem ipsum dolor sit amet, Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod Lorem ipsum dolor sit amet,

We start by understanding your risks and attack surface before recommending any tools or configurations. Security decisions are based on real threats, not trends or unnecessary features.

Our approach is grounded in real-world threat intelligence. We prioritize defenses against the attack vectors that are most likely to target your specific industry and tech stack.

Security solutions that scale with your business. We design systems that protect without slowing down your development velocity or creating unnecessary friction.

We believe in clear, jargon-free communication. You will always know what we are doing, why we are doing it, and how it impacts your security posture and bottom line.

We do not just wait for incidents. Our proactive monitoring and automated remediation catches issues before they become breaches, while our response team handles the rest.
Secure
Configure your infrastructure in your own cloud, using best practices, automatically.
Compliant
Get an audit trail of your SDLC from requirements, to development, to testing & deployment.
No Lock-in
You can cut off Coherence's access at any time — your infrastructure remains safe in your own cloud.
Scalable
Coherence makes sure your cloud is there for your users, and that you are avoiding surprise costs from automation.
Cost-effective
You get back engineering time and optimize your cloud deployments to lower your spend.
Developer-native
Builds and deployments are surfaced intuitively, empowering your team regardless of DevOps experience.
Call to Action Let’s Discuss with us
Get expert guidance from a security-first engineering team. No spam. No pressure. Just solutions.
Our Most Popular Blog
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod Lorem ipsum dolor sit amet,

Best IT Consultation
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod Lorem ipsum dolor sit amet,
Read More
